Like most, I advocate a password manager. And have frequently recommended 1Password (for years). However, I have led something of a double life in utilizing 1password without a subscription to store “important” passwords within a “local” iPhone vault. Whereas, I’d place my less critical credentials (think: Netflix) in LastPass for efficient cross platform access, including computer browser extension.
While 1password has never been breached and their technical architecture is actually fortified to keep our data secure in that scenario, experience tells us never say never – nothing is foolproof. But even if their cloud and our vaults remain secure, computer operating systems and browsers provide additional vectors of attack. Any random rogue browser extension can read everything (and I suspect how my Yahoo Mail address book was harvested, years ago) – including that 1password web view of your vault. Which is why I railed against 1password’s 2017 cloud requirement (which they wisely, thankfully backed off of).
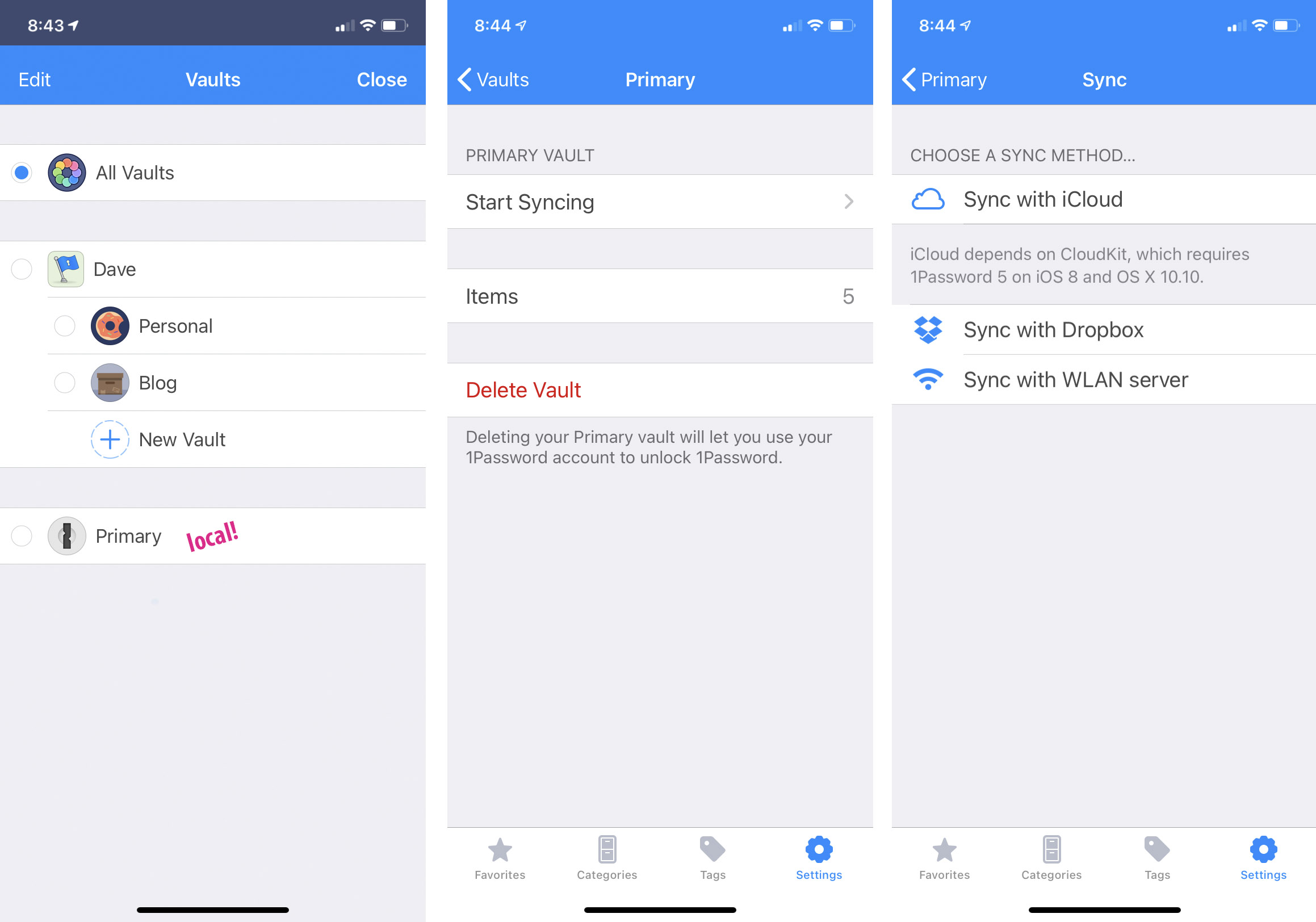
What I didn’t realize at that time, after they decided to support both cloud and local accounts, is that the two implementations can coexist. So, this week I finally subscribed to 1password ($36/yr) and was able to kick LastPass to the curb (with a clean, comprehensive import). Once 1password merged my existing passwords into a new cloud vault, I blew away the local vault, recreated it, and moved over financial institution and other sensitive credentials from cloud to iPhone. I just don’t want them anywhere on the web. (Then I emptied my 1password trash which, under normal circumstances, they conveniently retain for 12 months. “Local” iPhone vaults can optionally be backed up to iCloud or across the LAN, should one so choose.)
Beyond the above, as two-factor auth has taken off 1password has been a godsend in collocating those rotating 2fa codes alongside passwords and automagically pasting them to the clipboard as needed. No dedicated authenticator app required. (And many thanks to Adam for turning me onto this feature a year or so ago!)
Why not Last Pass for everything?
There are many elements of the LastPass interface I prefer, but a local vault is a requirement for me and I don’t believe they offer that. I also don’t believe they provide two-factor codes within each entry. While not originally a requirement, now I’m never going back – despite the reasonable argument against putting all eggs in one basket. LastPass also had a couple incidents and (based on Twitter friends) a history of questionable support, since being acquired.
Mike – LastPass stores your ‘vault’ in the cloud, with no option to keep your data strictly local. The advantage is that your passwords are synced across multiple devices, but there is some risk that your data could be hacked.
I am a LastPass user, but maybe I’ll check out 1Password in order to keep my most critical passwords (Google / Yahoo, which is the key to recovering everything else) off the cloud. Or I can go back to writing it on a Post It stuck under my keyboard. :)
Yeah, there was this whole meme mocking password notebooks on Twitter a few months back. Like physical paper notebooks. But that’s actually a reasonable, efficient, strong solution, especially for folks like my mom who are often intimidated by technology.
I get the best of both worlds now as a 1password subscriber – multiplatform with a nice browser extension for the credentials that don’t have the ability to destroy me and a local vault for those that do. :) Haven’t tried the ‘secure note’ feature yet – was bummed I couldn’t attach photos prior to the cloud account, but now I have some additional tools.
There’s definitely something to be said about a traditional paper interface for password storage for some people. I found out when visiting a couple years ago that my parents were using a single sheet of paper to list all of their online passwords. I extolled the virtues of 1Password, particularly with its browser integration, set them up with a 1-year free trial, installed it on their computers and phones, and copied all their passwords in for them. A year later I found out that they never really got into the habit of using 1Password, and were quite happy with their sheet of paper. Oh, well.
I’ve been using the standalone 1Password for years, still syncing via Dropbox. It works well enough, although sometimes getting the phone to pull down recent changes is a little wonky, requiring me to actually open the Dropbox app first before 1Password sees changes.
I get the concern about keeping everything local, and was originally this way several years ago. But ultimately, as long as you trust that there’s no fundamental flaw in their implementation of the vault encryption, you should be able to put your vault up on a public website as long as you use a strong enough key. The convenience of sync across multiple devices was too great to ignore, especially when on the go.
Regarding bank passwords in particular, the one thing I’ll never do is sign up for a service like Mint. I find that to be a far bigger risk than keeping my passwords encrypted in the cloud. Ultimately in order to login to bank websites, Mint must keep passwords in a form that is recoverable to plain text. Yes, it may be super-duper-double-triple encrypted as they imply on their “security” page, but that *has* to be reversible in order for their service to work. That makes them a *huge* target, and I feel like the risk of their database leaking is far higher than the risk of someone figuring out how to mathematically defeat the encryption on my password vault.
I’ve been meaning to take a look at BitWarden and see if it’s viable to migrate. It doesn’t get as much press as Lastpass, 1Password, KeePass, etc, but it seems to be very highly regarded in tech circles. Free, open source (with paid options for online hosting/sync). And apparently you can use your own sync server which is appealing.
I specifically do not use the MFA feature inside 1Password because it’s not really a second, separate form of authentication at that point. It is convenient but doesn’t add as much security as it could. I instead use Authy for MFA.
Lastpass at least has a separate app for MFA, which seems to separate MFA from the password vault, but I think Authy is still the better solution.
What about using Dropbox or iCloud for storage and sharing? Not as secure as local storage, but not a huge insecurity, no?
As Carlos noted, using the same app as your password vault and 2FA is a bad idea, because the whole point of 2FA is to store that second form of authentication in a separate spot. It’s true that 2FA in your password vault is a form of risk reduction, but I recommend using Authy, which is certainly less convenient, but if you’re going to do something do it right.
I’ve been using 1Password for years now without any cloud access. You can still purchase a desktop (no sub) license and just sync with your devices over your own network. It’s a great solution.
I did mention a few comments above that there’s a reasonable argument to be made against collocating rotating codes with their respective passwords. In fact, when Adam first turned me onto the feature, I was like hell no. But there’s that ever-present tension between convenience and risk. And, for me, for some accounts, I’ve made a choice – maybe not the best one, but at least it was a somewhat educated decision. Once again, the life altering accounts I have silo-ed – with codes in Google Authenticator. While Authy is probably the best code generator, Google requires no account and does not sync.
Authy syncing is a feature not a bug, because all your 2FA seeds are end-to-end encrypted. But if you’re happy with the increased convenience and reduced security, all power to ya’.
Got a Pixel 4a (Android 11) to replace my Moto G6 (Android 9) and now can sync with 1Password WLAN server on my Mac. AgileBits have not been very helpful. Trying to push me to a subscription instead. Only sync method w/o subscription on 1Password for Android now is WLAN server. No option to import a vault.